Now the hacking technology is so advanced that instead of just making software attacks on the system, attackers change the hardware itself.
Houman Homayoun
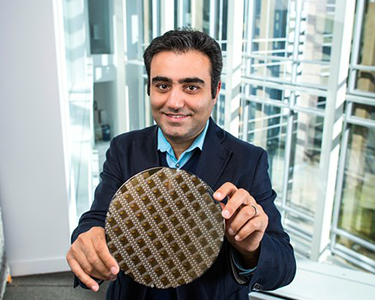
Houman Homayoun and his team are developing new hardware security defenses.
National security is at risk because of a war on hardware, according to a Mason Engineering researcher.
Many cybersecurity attacks today are targeting hardware, and these invasions are dangerous and difficult to defend, says Houman Homayoun, an assistant professor of electrical and computer engineering.
Experts have been using different strategies to protect software from hackers for more than 20 years. "Now the hacking technology is so advanced that instead of just making software attacks on the system, attackers change the hardware itself," Homayoun says.
"Hardware security is emerging as a new field that is needed to address the enormous challenges government and industry are facing to protect integrated circuits used in areas such as the Internet of Things and cloud infrastructures.”
To improve hardware security, Homayoun has received more than $3 million in funding from multiple government research programs.
Part of the reason for the increase in hardware security problems is that many semiconductor chips are no longer manufactured in the United States but are made overseas, including in Europe and Asia, he says.
Some untrustworthy manufacturers are inserting hardware Trojans, a type of malware, into integrated circuits when they are fabricating them, and some are copying and cloning sensitive chips. “They can steal the technology completely because they know every detail of the design to fabricate it, which means they don’t have to spend time and money designing their own defense technology,” he says.
This is a problem for national security because many chips are used in important military equipment, including intercontinental ballistic missiles.
The U.S. government is combatting these problems in several ways, including identifying trustworthy manufacturers.
Homayoun’s research team members, including 14 PhD students, six master’s students, one postdoctoral student and two undergraduates, are developing new hardware security defenses designed to help protect against hacking of integrated circuits, cloning of chips, and securing processor architecture.
Homayoun says it’s difficult to detect if an integrated circuit has been hacked because the Trojan is manufactured into the hardware. “It sits side-by-side the hardware. You need very expensive equipment to catch it.”
His group is using machine learning, at both the hardware and software levels, to work on this problem, which means they are programming the computer to learn from past attacks to predict future ones. “We want to make it more difficult and more expensive for the attacker to insert Trojans and to clone the chip,” he says. “But there is no absolute security.”
The problem with machine learning is that both sides are using it, Homayoun says. “We are using it to detect what they are going to do in the future, and they are using it to be able to detect and understand what we are doing to defend so they can bypass our defense in the future.”
The key is to stay one step ahead of them, he says.
The researchers also are looking for ways to stop companies from reverse engineering, which is figuring out the design of the chip so they can make a reproduction of it. “We are trying to prevent the manufacturer from finding out the entire recipe for our chip. To do that, we only give them part of the recipe for making it so they can’t fabricate it.”
He says there is a lot more work to be done in this field including training hardware security warriors. "While software security and relevant fields have been around for at least two decades, hardware security is a new field with enormous research challenges, especially given the lack of enough hardware security experts in both industry and government.”

Houman Homayoun's research team is looking for ways to stop companies from reverse engineering, which is figuring out the design of the chip so they can make a reproduction of it.
We want to make it more difficult and more expensive for the attacker to insert Trojans and to clone the chip. But there is no absolute security.
Houman Homayoun
